Effective PKI automation is essential for enhancing security and operational efficiency in the digital landscape. It minimizes manual tasks, reduces errors, and facilitates quick certificate deployment. Organizations can achieve significant benefits, such as improved compliance and reduced bottlenecks. However, common challenges like inventory management and human error necessitate strategic approaches. By implementing best practices and leveraging advanced technologies, businesses can supercharge their PKI efforts. There are further insights and strategies waiting to be explored to maximize https://aquipress.com/top-rated-pki-management-platform-unveiled/ PKI automation's impact.
Key Takeaways
- Implement automated certificate management tools to reduce manual intervention and enhance efficiency in PKI processes. Establish rigorous policies and protocols for identity verification to strengthen security during certificate issuance. Utilize predictive analytics through machine learning to anticipate and mitigate potential PKI issues proactively. Conduct regular audits and compliance checks to ensure adherence to security standards and enhance operational transparency. Embrace cloud-based PKI solutions to support scalability and adaptability in a rapidly evolving digital environment.
Understanding Public Key Infrastructure (PKI)
Although often overlooked, Public Key Infrastructure (PKI) plays an essential role in digital security by facilitating secure communications and transactions over networks.
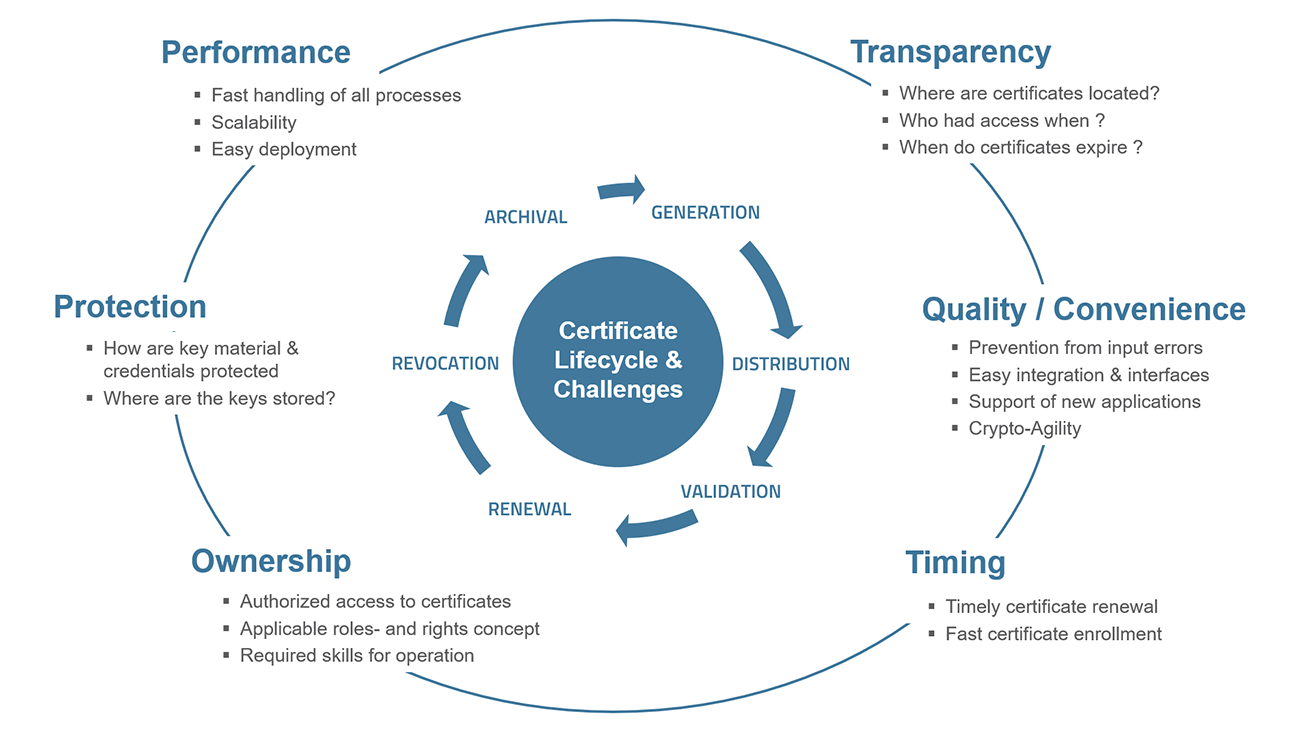
PKI is a framework that enables the creation, management, distribution, and revocation of digital certificates, which authenticate the identities of users, devices, and applications. It relies on asymmetric cryptography, utilizing a pair of keys—public and private—to encrypt and decrypt data securely.
Certificates issued by trusted Certificate Authorities (CAs) serve as digital signatures, ensuring the integrity and confidentiality of information exchanged online. By establishing a trust hierarchy, PKI underpins various security protocols, such as SSL/TLS for secure web browsing and email encryption.
This foundational technology is critical for protecting sensitive data in an increasingly interconnected digital landscape.
The Importance of PKI Automation
As organizations increasingly rely on digital communications, the automation of Public Key Infrastructure (PKI) becomes essential for maintaining security and efficiency.
Manual PKI processes can lead to delays, human errors, and vulnerabilities, undermining the integrity of digital transactions. Automation streamlines certificate management, ensuring timely issuance, renewal, and revocation, which is critical in preventing potential security breaches.
Manual PKI processes introduce risks; automation ensures efficient certificate management and strengthens digital transaction integrity.
Furthermore, the complexity of managing cryptographic keys escalates as organizations scale, making automated solutions crucial for effective oversight.
By implementing PKI automation, organizations can enhance their security posture, facilitate compliance with regulatory standards, and support rapid digital growth.
Ultimately, embracing PKI automation not only protects sensitive information but also fosters a more resilient and agile digital environment.
Key Benefits of Automating PKI
PKI automation offers several key benefits that greatly enhance organizational efficiency and security.
By streamlining the certificate lifecycle management, organizations can reduce the time and resources spent on manual tasks, allowing IT teams to focus on more strategic initiatives. Automated processes minimize the risk of human error, ensuring that critical security protocols are consistently enforced.
Additionally, automation facilitates rapid deployment of certificates, enabling organizations to adapt quickly to changing security requirements. Improved visibility and reporting capabilities further enhance compliance efforts, making it easier to meet regulatory obligations.
Common Challenges in Manual PKI Management
Manual PKI management presents significant challenges, particularly with regard to time consumption and security vulnerabilities.
The processes involved can be labor-intensive, leading to inefficiencies that hinder organizational growth.
Additionally, the reliance on manual methods increases the risk of security breaches, making automation a critical consideration for businesses.
Time-Consuming Processes
How can organizations effectively manage their Public Key Infrastructure (PKI) without succumbing to the pitfalls of time-consuming processes?
Manual PKI management often involves labor-intensive tasks such as certificate issuance, renewal, and revocation, which can drain valuable resources. Organizations frequently face delays due to the intricate approval workflows required for certificate management, leading to increased operational inefficiencies.
Additionally, tracking and maintaining an accurate inventory of certificates can become overwhelming, especially in large environments. This cumbersome process not only hinders responsiveness but also increases the risk of human error.
Increased Security Risks
Inefficiencies in PKI management can lead to heightened security vulnerabilities. Manual processes often suffer from human errors, such as misconfigurations or overlooked certificate renewals, which can expose organizations to significant risks.
Additionally, the complexity of managing cryptographic keys and certificates without automation increases the potential for unauthorized access or data breaches. As organizations scale, the challenge of maintaining an accurate inventory of digital assets becomes more pronounced, making it harder to guarantee compliance with security policies.
Moreover, delayed responses to incidents and lack of real-time monitoring can exacerbate these risks. In an era where cyber threats are evolving rapidly, relying on manual PKI management poses a considerable challenge to maintaining a robust security posture.
Strategies for Effective PKI Automation
Although implementing a Public Key Infrastructure (PKI) can seem intimidating, adopting effective automation strategies can greatly enhance its efficiency and reliability.
Organizations should prioritize establishing clear policies and procedures that outline roles, responsibilities, and workflows. Leveraging automated certificate management tools can streamline the issuance, renewal, and revocation processes, reducing human error and improving response times.
Regular audits and monitoring of PKI activities are essential to guarantee compliance and identify potential vulnerabilities. Integrating machine learning algorithms can also provide predictive analytics, helping organizations stay ahead of security threats.
Finally, investing in training and resources for IT teams guarantees they are well-equipped to manage the automated infrastructure, ultimately fostering a more secure and resilient digital environment.
Integrating PKI Automation With Existing Systems
Integrating PKI automation with existing systems is essential for achieving seamless compatibility across various platforms.
This integration not only streamlines workflow processes but also enhances overall security protocols, ensuring that organizations can effectively manage their digital identities.
A well-executed integration can considerably contribute to operational efficiency and risk mitigation.
Seamless System Compatibility
How can organizations guarantee that their Public Key Infrastructure (PKI) automation seamlessly integrates with existing systems? To achieve this, organizations must prioritize compatibility during the planning phase of PKI implementation.
Conducting a thorough assessment of existing systems and identifying potential integration points is essential. Leveraging standardized protocols and APIs can facilitate smoother interactions between PKI solutions and legacy systems.
Additionally, organizations should engage in rigorous testing to ascertain interoperability, minimizing disruptions during deployment. Training staff on new PKI tools enhances understanding and reduces resistance to change.
Ultimately, fostering collaboration among IT teams and stakeholders assures that the PKI automation aligns with organizational objectives, paving the way for a more cohesive digital environment.
Streamlined Workflow Integration
As organizations seek to enhance their operational efficiency, the integration of Public Key Infrastructure (PKI) automation into existing workflows becomes essential. This process allows for the seamless management of digital certificates and keys, reducing manual tasks and minimizing human error.
By incorporating PKI automation, organizations can streamline their certificate lifecycle management, ensuring timely issuance, renewal, and revocation of certificates.
Additionally, integration with existing systems facilitates better data flow and collaboration among departments, ultimately leading to faster response times and improved service delivery.
Businesses can leverage automation tools to achieve consistency in processes, enabling teams to focus on more strategic initiatives rather than routine administrative tasks.
Enhanced Security Protocols
What strategies can organizations adopt to strengthen their security protocols?
Integrating Public Key Infrastructure (PKI) automation with existing systems is a critical approach. Organizations should first conduct a thorough assessment of their current security landscape to identify vulnerabilities.
Next, they can implement automated certificate management solutions to guarantee timely renewals and minimize risks associated with expired certificates.
Enhancing user authentication through multi-factor authentication (MFA) and robust encryption mechanisms further fortifies security.
Additionally, organizations should establish clear policies for access control and regularly update their systems to combat emerging threats.
Best Practices for PKI Security
Implementing robust best practices for PKI security is essential for organizations aiming to protect their digital assets.
First, organizations should guarantee rigorous identity verification processes for all certificate requests, minimizing the risk of unauthorized access. Regularly updating and patching PKI software helps mitigate vulnerabilities.
Additionally, employing strong cryptographic algorithms and key lengths enhances security against potential attacks. Organizations should also establish a detailed certificate lifecycle management protocol, including timely renewals and revocations.
Employing robust cryptographic algorithms and effective certificate lifecycle management is vital for enhancing PKI security.
Utilizing hardware security modules (HSMs) for key storage adds an extra layer of protection.
Finally, conducting regular audits and assessments of PKI systems can identify weaknesses and guarantee compliance with industry standards, thereby maintaining a secure PKI environment that supports overall organizational integrity.
Measuring the Success of PKI Automation
Measuring the success of PKI automation involves evaluating key performance indicators that reflect the system's effectiveness.
Additionally, a thorough cost efficiency analysis and time savings evaluation can provide insights into the overall impact of automation on organizational resources.
These metrics are essential for determining the value added by PKI automation in driving digital growth.
Key Performance Indicators
Establishing key performance indicators (KPIs) is essential for evaluating the effectiveness of PKI automation initiatives. By defining measurable goals, organizations can assess the impact of automation on their digital security posture.
Common KPIs include certificate issuance time, the number of automated versus manual processes, and the reduction in human errors. Tracking these metrics allows organizations to identify bottlenecks and optimize workflows.
Additionally, measuring user satisfaction with the PKI system can provide insights into the effectiveness of the automation efforts. Regularly reviewing these KPIs enables organizations to make informed decisions, driving continuous improvement in PKI automation.
This strategic approach not only enhances security but also supports broader digital growth objectives.
Cost Efficiency Analysis
Cost efficiency plays a pivotal role in evaluating the overall success of PKI automation initiatives. Organizations can assess cost efficiency by analyzing the reduction in operational expenses associated with certificate management, including labor costs, system maintenance, and potential security breaches.
By automating processes such as certificate issuance and renewal, organizations can minimize human error and streamline workflows, ultimately driving down costs. Additionally, the deployment of automated PKI solutions can lead to better resource allocation, allowing IT teams to focus on strategic tasks rather than routine certificate management.
Thorough audits of spending before and after automation implementation can further highlight financial benefits, making it easier for organizations to justify investments in PKI technology as a means of enhancing cost efficiency.
Time Savings Evaluation
While organizations seek to enhance their operational efficiency, evaluating time savings from PKI automation becomes essential in determining its overall impact.
By automating tasks such as certificate issuance, renewal, and revocation, organizations can considerably reduce the time staff spend on manual processes. This streamlined approach not only minimizes human error but also accelerates service delivery.
Quantifying these time savings involves analyzing workflow improvements and comparing pre-automation and post-automation metrics. Additionally, organizations should consider the opportunity costs associated with freed-up resources, enabling teams to focus on strategic initiatives rather than routine maintenance.
Ultimately, a thorough time savings evaluation provides a clear picture of how PKI automation contributes to organizational agility and digital growth.
Future Trends in PKI and Automation
The future of Public Key Infrastructure (PKI) and automation is poised for significant transformation, driven by emerging technologies and increasing security demands. Organizations are expected to adopt innovative solutions to enhance their PKI systems, ensuring scalability and efficiency.
Key trends shaping this future include:
Integration with Artificial Intelligence: AI will streamline certificate management and anomaly detection, improving security posture. Blockchain Technology: Utilizing blockchain for PKI can enhance trust and transparency in digital transactions. Zero Trust Architecture: The shift towards zero trust will necessitate more robust PKI systems to verify user identities continuously. Cloud-Based PKI Solutions: Cloud adoption will drive demand for flexible, cost-effective PKI solutions that support remote work environments.These trends indicate a dynamic evolution in the PKI landscape.
Case Studies: Organizations Thriving With Automated PKI
Organizations are increasingly leveraging automated PKI systems to boost security and efficiency, aligning with the trends of integrating advanced technologies.
For instance, a leading financial institution adopted automated PKI to streamline certificate management, reducing provisioning time by 70% while enhancing compliance with regulatory standards.
Similarly, a healthcare provider implemented automated PKI to secure patient data, considerably lowering the risk of data breaches and ensuring patient confidentiality.
In the retail sector, a global e-commerce company utilized automated PKI to secure online transactions, increasing customer trust and satisfaction.
These case studies illustrate how automated PKI not only enhances security but also drives operational efficiency, enabling organizations to thrive in a digital-first landscape.
The results highlight the transformative potential of PKI automation.
FAQ
What Is the Cost of Implementing PKI Automation?
The cost of implementing PKI automation varies greatly based on factors such as organization size, existing infrastructure, and specific requirements.
Initial expenses may include software licensing, hardware, and integration services, alongside ongoing maintenance and support fees.
Organizations may also encounter costs related to training personnel and potential disruptions during the change period.
Ultimately, a thorough cost-benefit analysis is essential for determining the total investment necessary for successful PKI automation implementation.
How Long Does It Take to Automate PKI?
Automating Public Key Infrastructure (PKI) can vary greatly in duration, akin to the difference between a quick sprint and a marathon.
Typically, the process may take anywhere from a few weeks to several months, depending on the organization's size, complexity, and existing infrastructure.
Factors such as resource availability and the integration of necessary tools play vital roles.
Ultimately, the timeline reflects the balance between thoroughness and speed in achieving a streamlined PKI system.
Can PKI Automation Be Customized for Specific Industries?
PKI automation can indeed be customized for specific industries. Each sector, such as healthcare, finance, or manufacturing, has unique security requirements and regulatory compliance needs.
What Skills Are Needed for Effective PKI Management?
Effective PKI management requires a combination of technical and analytical skills. Proficiency in cryptography and security protocols is essential, alongside a deep understanding of network infrastructure and systems administration.
Additionally, strong problem-solving abilities and attention to detail are vital for troubleshooting and maintaining PKI systems. Familiarity with regulatory compliance and risk management also enhances one's capacity to manage PKI effectively, ensuring secure and efficient digital communication within an organization.
How Do We Handle PKI Automation Downtime or Failures?
In a bustling city, a traffic light system failed, causing chaos at intersections.
Similarly, when handling PKI automation downtime, organizations must have a contingency plan in place. This includes regular backups, a clear communication strategy, and pre-defined recovery procedures.
Conclusion

In an era where 82% of data breaches involve compromised credentials, the need for robust Public Key Infrastructure (PKI) automation has never been more crucial. By streamlining PKI processes, organizations not only enhance their security posture but also drive digital growth. Embracing effective automation strategies not only mitigates common challenges but positions businesses to thrive in an increasingly complex digital landscape. As the future unfolds, automated PKI will be essential in safeguarding critical information and fostering innovation.